News Story
Gang Qu and colleagues develop method to detect recycled integrated circuits masquerading as new chips
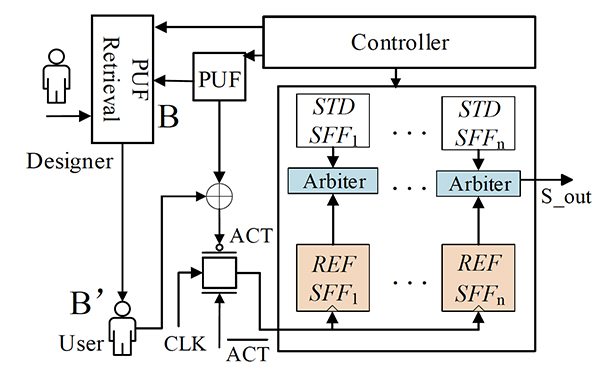
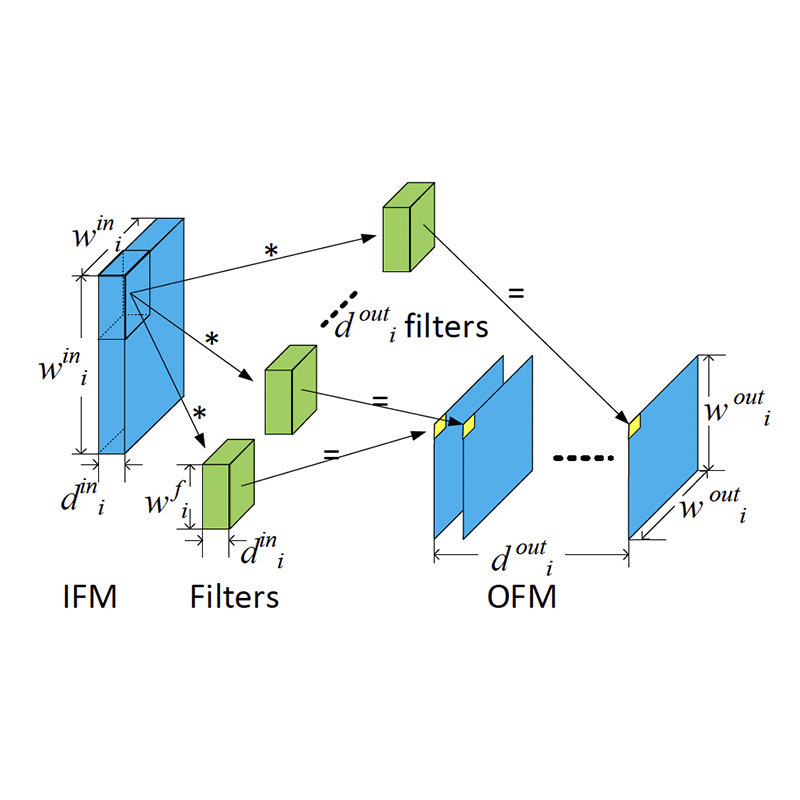
An illustration of the detection process: a user obtains the unlock key from the designer, and the authentication module will output an ‘ACT’ signal to the transmission gate so that the clock signal can be given to the reference-SFF’s clock port. When the aging sensor is activated, it will give the detection result. (Fig. 1 from the paper)
The electronics industry is a major target of counterfeiting, which causes tens of billions of dollars of losses to the industry every year. Semiconductor chips, including integrated circuits (ICs), are highly vulnerable. Surprisingly, one of the ways ICs can be counterfeited is through recycling—something that usually has a positive reputation.
Recycled ICs do not have the same performance and service lifetime of the new chips they are falsely claimed to be, which poses a threat to reliability of the electronic systems in which they are placed.
In a paper presented virtually this fall at the Association of Computing Machinery Great Lakes Symposium on VLSI 2020 (GLSVLSI ’20), Professor Gang Qu (ECE/ISR) and his colleagues Zhichao Xu and Aijiao Cui of the School of Electronic and Information Engineering at Harbin Institute of Technology in Shenzhen, China, proposed a way to detect recycling that can be built right into the design of ICs.
IC counterfeiting can be divided into three categories: cloning, overbuilding, and recycling. Cloned ICs are fabricated by an adversary after detailed design information of the original IC is obtained by illegal reverse engineering. During the process of IC cloning, an adversary may make changes to the IC either to slightly modify the functionality or just to disguise the cloning behavior. Tampered and remarked ICs also are considered cloned ICs. Overbuilding refers to cases where a dishonest foundry fabricates more chips than it is paid to make and sells the extra copies in the grey market, normally under a lower price, to make profits. Both cloning and overbuilding are malicious by nature.
However, IC recycling can either be an effective and environmental friendly way to reuse chips that are becoming obsolete, or a dangerous way to counterfeit. On the legitimate side, when a chip in a mission critical system ages and its performance becomes inadequate, it or some of its parts can be removed and used in other, non-mission critical applications. Even chips that no longer work can be harvested for their valuable metals such as gold, silver, and copper—which is good for the environment.
The problem arises when malicious actors clean and polish existing ICs, recycle them and release them into the market branded as “new.” As more chips are replaced and upgraded earlier than their designed life cycle because of market competition, this malicious IC recycling has become a serious problem. While recycled chips may still have great value left in them, passing them off as new can result in disastrous consequences for the systems in which they are placed.
In their paper, A New Aging Sensor for the Detection of Recycled ICs, Qu, Xu and Cui propose incorporating a scan chain-based aging sensor into an IC design that will enable users who have been given an “unlock key” to distinguish recycled from “fresh” ICs.
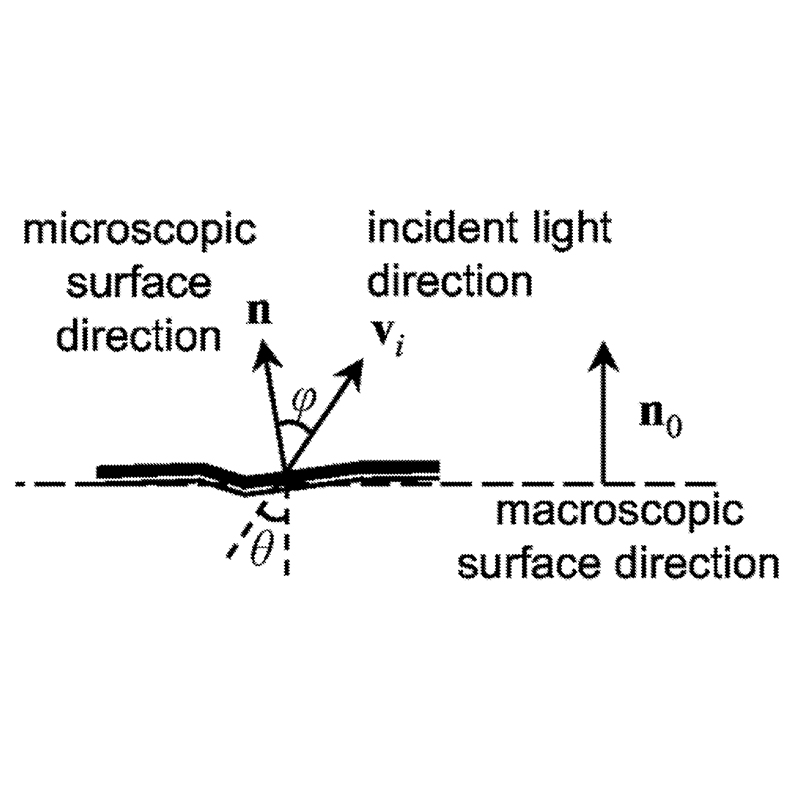
Their method is based on the time-delay variation between normal stressed circuit structure and the reference circuit structure. An authentication module generates the unlocking signal of the reference circuit clock. When the user enters the correct key, the authentication module will generate an ‘ACT’ signal to the clock port of circuit-ref such that it can perform the comparison analysis. Simulation data shows a strong functional relationship between the aging time and the aging rate.
The proposed mechanism can accurately detect a recycled IC at a very low cost and can resist typical attacks. Because this approach reuses the scan chain structure of the chip, its hardware overhead is very small. Future work will explore the application of this approach in secure and sensitive scenarios.
Published November 9, 2020